This post is inspired by a popular tech YouTuber teaching what is essentially a reverse proxy. While there is a time and a place for such technologies, your home network is not one of them.
He starts off by saying you have a lot of stuff at home and you might want to give access to friends and family to things like Plex or your NAS. I have some of these things but access is limited. Here’s how I do it: Internal DNS & VPNs.
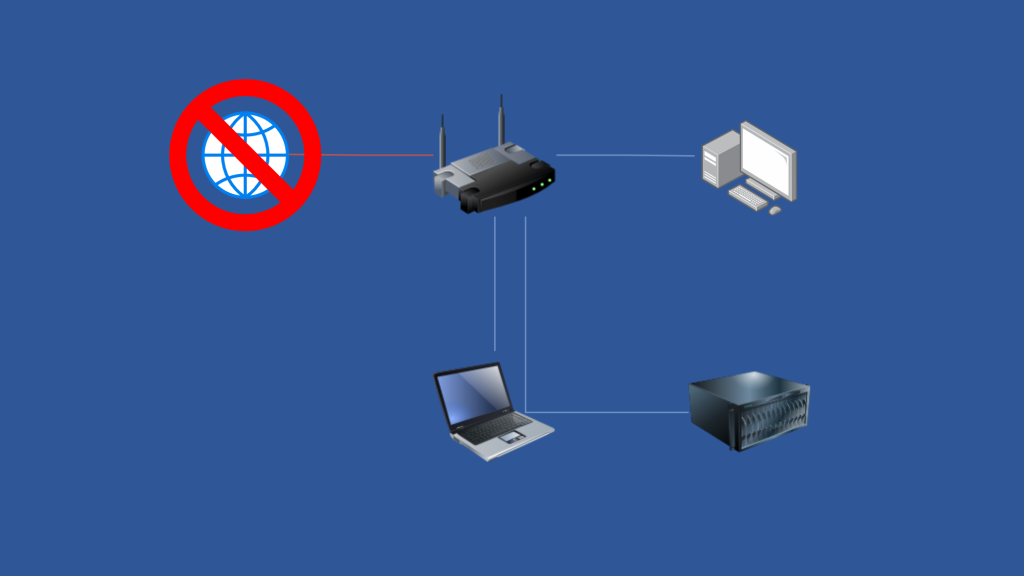
Why you shouldn’t open ports to the world
The internet is a dangerous place. There are bots, script kiddies, and hackers looking for weaknesses. When you host services on your internal network, even using Cloudflare, you have to open a port. Someone is going to find this port. Even if your ISP blocks 80/443. 8080 is commonly used as a subsitute as well as 8443, 9443, etc.
I’m also going to go out on a limb and say you’re not running a proper DMZ – that is, it’s securely isolated from your main network.
Even if you have a reverse proxy on this port, it’s still not hard to get in and see what you have running. And if your reverse proxy isn’t properly protected, it can be taken over and used as a gateway into your home network.
What’s a better way
Ultimately, not exposing anything you don’t have to. But if you do want to give your friends or family access, try a VPN solution first. With my family, we have a site-to-site VPN setup. So we’re all on the same network even though we’re not. My internal DNS works from my parents’ house so I can pull up internal websites. I can stream from my computer if I want to. When I’m not at home, I run a Wireguard VPN which puts me on my home network. My Wireguard server is exposed, but in a restricted VLAN.
For those situiations where you can’t get by with a VPN, do the next best thing – a reverse proxy not hosted in your house. This is what I do for some websites that actually are hosted in my house. I actually have a site-to-site VPN setup at a data center to an OPNSense firewall from my house. This tunnel only allows the restricted public VPN traffic and over ports 80/443 (or whatever port a service uses like 8090, etc.).
The reverse proxy is also behind a restricted firewall that is doing some packet filtering. It’s also on a data center network. This means the connection is reliable. While the connection can be interrupted by my home network being down, I can easily change where the server points to – like if I migrate it to a newer server or to a maintenance page.
It’s fine to host stuff in your house, just don’t open your house to the world!